Wonk post: chosen ciphertext security in public-key encryption (Part 2) – A Few Thoughts on Cryptographic Engineering
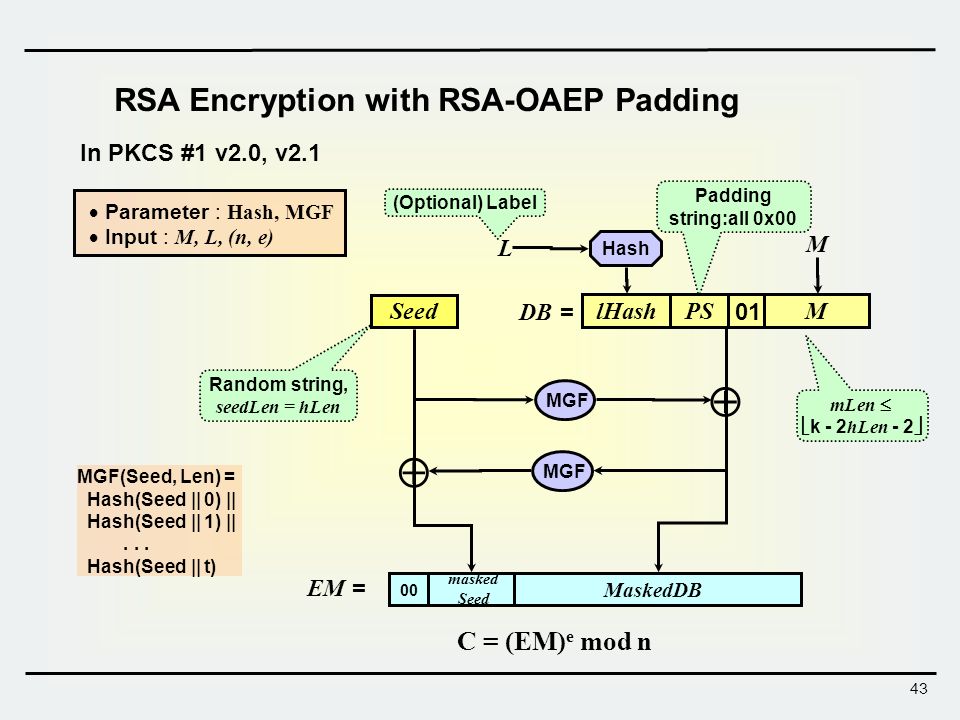
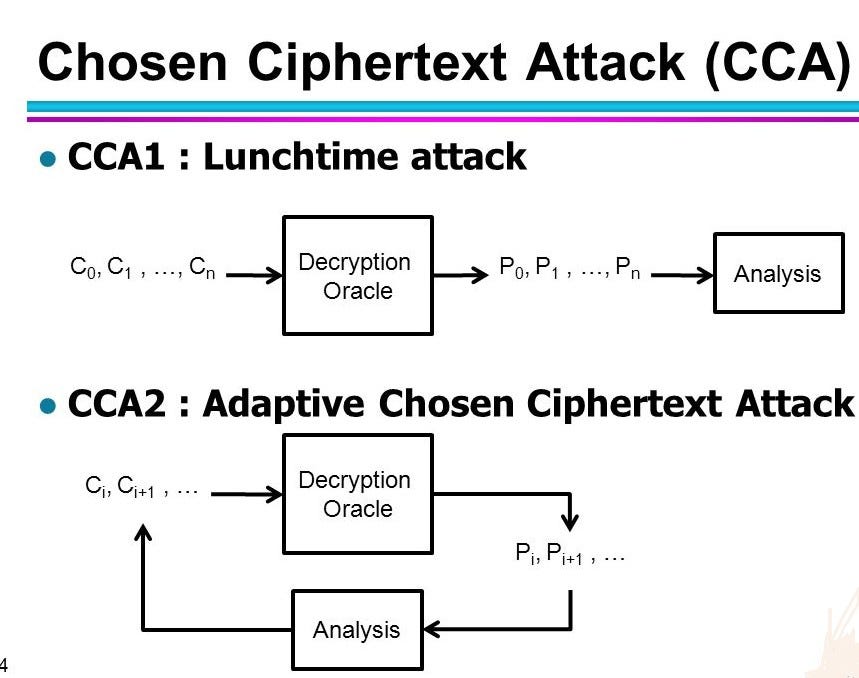
Introduction to Information Security Lecture 4: Public Key Cryptography & Digital Signature Prof. Kwangjo Kim. - ppt download
GitHub - mbakkar/OAEP: An implementation of optimal asymmetric encryption padding, to be used in conjunction with RSA.




![PDF] What Hashes Make RSA-OAEP Secure? | Semantic Scholar PDF] What Hashes Make RSA-OAEP Secure? | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/4d96ea89cbb277af3ebfb552ece3be8c038d0797/10-Figure2-1.png)

![PDF] What Hashes Make RSA-OAEP Secure? | Semantic Scholar PDF] What Hashes Make RSA-OAEP Secure? | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/4d96ea89cbb277af3ebfb552ece3be8c038d0797/11-Figure3-1.png)
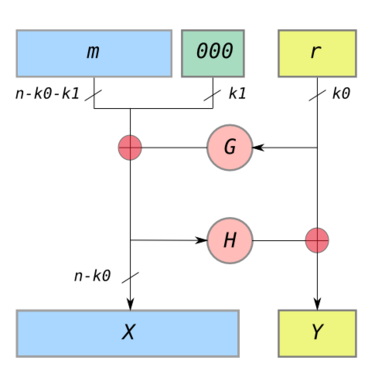
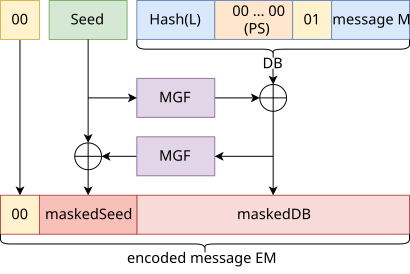
![PDF] What Hashes Make RSA-OAEP Secure? | Semantic Scholar PDF] What Hashes Make RSA-OAEP Secure? | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/4d96ea89cbb277af3ebfb552ece3be8c038d0797/8-Figure1-1.png)